Image credit: Digital Transformation Agency
The Australian Government has released a draft
of the Trusted Digital Identity
Framework, following a period of consultation with
government, industry and privacy representatives. The Government is seeking
public comment on the draft national standards and rules that will frame
the Australian Government’s digital identity program.
Assistant Minister for Digital Transformation, Angus Taylor,
said, “The framework sets out a nationally-consistent approach to how digital
identity will be managed.”
The Framework will give people the choice to set up a
digital identity once, and complete their business with a range of online
government services rather than visiting a shop front.
This is a “federated” style identity system, which refers to
a decentralised model enabling individuals to access public and private sector
services through a choice of identity provider. This is as opposed to a
syndicated system a single identity credential is issued, typically by
government, to provide single sign-on access to public and private sector
services.
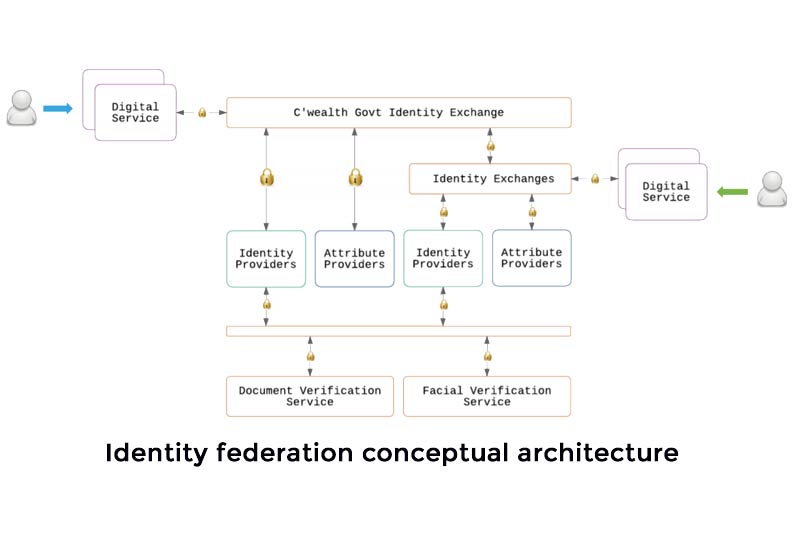
(In the image above the article demonstrating the Identity Federation Conceptual Architecture, Identity is defined combination of identity attributes which uniquely distinguishes a person within a specific context. While Identity Attribute is a piece of information relating to identity. E.g. Name or Date of Birth.
Identity Service Providers verify the identity of individuals, bind an identity to an authentication credential and assert identity to other members of the identity federation.
Identity Exchange conveys, manages and coordinates the flow of identity attributes and assertions between members of the identity federation. Once an Identity Exchange has been granted accreditation it becomes a trusted core element of the identity federation. Identity Service providers also undergo accreditation.
Accreditation is the procedure by which an authoritative body gives independent attestation conveying formal demonstration of a Service Provider’s competence to provide services of the kind specified in an assurance framework.)
The Trust Framework addresses the following functional
responsibilities:
- Governance and Policy
Development: Developing and amending policies; decision making;
stakeholder-facilitation; managing standards and procedures; accountability
mechanisms. - Policy Enforcement:
Ensuring compliance with Trust Framework standards and requirements;
enforcement mechanisms; performing assessments or audits; managing policy
changes and releases. - Participating Entity
Management: Administration and enrolment of participating entities;
accreditation/on-boarding; support; dispute resolution. - Network Evolvement:
Growing and supporting the identity eco-system; marketing; communication and
strategy developing. - Trust Framework
Operations: Offering central services to the participating entities and/or
public, e.g. information and discovery services
People can provide feedback on just one or all of the 14
documents [1] that make up the framework and define minimum requirements (the
rules) and recommended approaches (the tools). This includes documents outlining how providers
will be accredited, privacy, security, risk and fraud management requirements,
as well as standards for usability and accessibility.

The draft Trusted Digital Identity Framework is available
for feedback until 8 December 2017 at the Digital Transformation Agency website.
The framework sits alongside the Digital Transformation
Agency’s Govpass technology platform, which is currently in private
beta. GovPass aims
to make the process of proving who you are to government services online
simple, safe and secure. The Govpass platform will be tested with a broader
number of users and services in the first half of 2018.
[1] The fourteen documents include:
- Trust Framework
Structure and Overview - Trust Framework
Accreditation Process - Glossary of Terms
- Privacy Assessment
- IRAP Assessment
- Core Privacy
Requirements - Core Protective
Security Requirements - Core User Experience
Requirements - Core Risk Management
Requirements - Core Fraud Control
Requirements - Digital Identity
Proofing Standard - Digital Authentication
Credential Standard - Information Security
Documentation Guide - Risk Management Guide
















